Proxy vs Reverse Proxy: 7 Key Differences + Apache & Nginx Examples
When people search for proxy vs reverse proxy, they usually want a quick answer. Instead, they land in a maze of technical jargon. Let’s clear that fog and make it simple, practical, and actually useful.
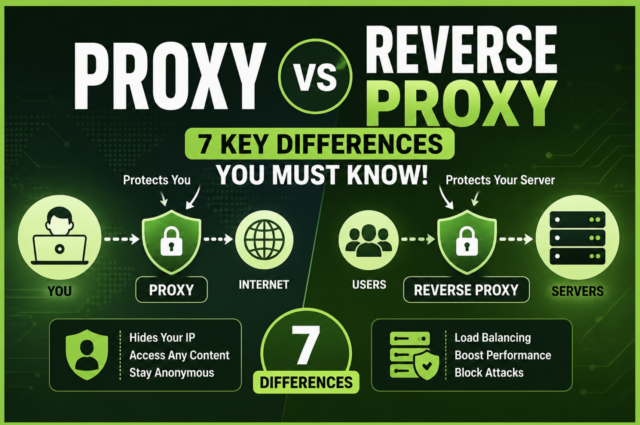
A proxy is your mask. A reverse proxy is the system’s shield.
But once you add tools like Apache HTTPD reverse proxy or Nginx forward proxy, things get even more interesting. Let’s walk through it like a story, not a textbook.
 What Is a Proxy?
What Is a Proxy?
A proxy, often called a forward proxy, sits between you and the internet. It takes your request, sends it forward, then brings the answer back.
Simple flow:
User → Proxy → Website → Proxy → User
This is why people also search for:
- forward proxy and reverse proxy
- forward and reverse proxy
A forward proxy works on behalf of the client. It’s your digital representative.
Why proxies are used
- Hide your IP
- Access blocked content
- Manage multiple accounts
- Run automation tools
- Scrape websites safely
If you run SEO tools or automation scripts, you already rely on proxies daily. Services like https://buyproxies.org help distribute requests across multiple IPs so everything looks natural.
What Is a Reverse Proxy Server?
A reverse proxy server flips the entire concept.
Instead of standing in front of the user, it stands in front of servers.
Flow:
User → Reverse Proxy → Backend Server
The user never talks directly to the server. The reverse proxy decides what happens next.
Why reverse proxies exist
- Load balancing traffic
- Protecting servers from attacks
- Speeding up websites with caching
- Hiding backend infrastructure
This is where tools like Apache HTTPD reverse proxy and Nginx reverse proxy setups come into play.
Forward Proxy and Reverse Proxy Explained Simply
Here’s the clean distinction:
- Forward proxy → hides the client
- Reverse proxy → hides the server
It’s like sending a messenger versus building a guarded gate.
Both solve problems. Just different ones.
7 Key Differences Between Proxy and Reverse Proxy
1. Network Position
Forward proxy sits near the user
Reverse proxy sits near the server
This single shift changes everything.
2. Who They Represent
Forward proxy represents you
Reverse proxy represents the server
One speaks for you. The other speaks for the system.
3. Traffic Direction
Forward proxy handles outgoing traffic
Reverse proxy handles incoming traffic
Think of one pushing requests out and the other filtering them in.
4. Security Role
Forward proxy protects identity
Reverse proxy protects infrastructure
One hides your face. The other hides the building.
5. Performance
Forward proxies can help scale scraping and automation
Reverse proxies improve speed using caching and load balancing
6. Use Cases
Forward proxy:
- SEO scraping
- Social media automation
- Geo testing
- Privacy browsing
Reverse proxy:
- Hosting large websites
- API management
- Enterprise applications
- Traffic distribution
7. Real World Setup
A modern system often uses both:
User → Forward Proxy → Internet → Reverse Proxy Server → Backend
Layered like armor over armor.
Apache Proxy and Apache HTTPD Reverse Proxy
Apache is not just a web server. It can act as both a forward and reverse proxy.
Apache reverse proxy example use cases
- Route traffic to multiple backend servers
- Secure internal applications
- Create a single entry point for complex systems
Search terms like apache proxy and apache httpd reverse proxy exist because Apache is widely used in enterprise setups.
Apache modules like mod_proxy and mod_proxy_balancer handle these tasks behind the scenes.
Nginx Forward Proxy and Reverse Proxy
Nginx is like a traffic conductor with laser focus.
Nginx reverse proxy
- Extremely fast
- Handles high traffic
- Used by large-scale platforms
Nginx forward proxy
Less common but still used, especially in controlled environments.
Searches like:
- forward proxy nginx
- nginx forward proxy
show that developers want flexible control over outgoing traffic too.
When to Use a Forward Proxy
Use a forward proxy when you need control over outgoing requests.
Typical scenarios:
- Running bots or automation tools
- Managing multiple social accounts
- Scraping search engines
- Testing content from different countries
Without proxies, your IP gets flagged quickly. With them, your traffic looks like a crowd instead of a single loud voice.
When to Use a Reverse Proxy Server
Use a reverse proxy when you manage servers or applications.
Typical scenarios:
- Handling large traffic spikes
- Protecting servers from attacks
- Improving site speed
- Scaling infrastructure
Reverse proxies are invisible heroes. Users never see them, but they keep everything alive.
Forward and Reverse Proxy Together
This is where things get powerful.
Imagine this flow:
User → Forward Proxy → Internet → Reverse Proxy → Server
You get privacy, control, performance, and security all at once.
It’s like wearing armor while also guarding the castle.
Common Mistakes
Confusing forward proxy and reverse proxy
They are not interchangeable
Using cheap proxies
Low quality proxies get blocked fast
Ignoring infrastructure
Reverse proxies need proper setup to shine
Overcomplicating things
Start simple, then scale
SEO Insight
Understanding forward proxy and reverse proxy is valuable beyond tech.
It helps with:
- SEO scraping strategies
- Website speed optimization
- Security improvements
- Infrastructure planning
Search engines reward fast, stable websites. Reverse proxies help with that.
Data collection tools rely on forward proxies to function properly.
Final Thoughts
Proxy and reverse proxy are like two sides of a coin, but each side faces a different direction.
Forward proxy gives you freedom.
Reverse proxy gives systems stability.
Once you understand both, you stop guessing and start building smarter systems.

